How to Talk to AI
The real skill is clear thinking, not prompting or context

At Fyodor‘s talk last week at Blackhat he talked about the research he’s been doing, and the ways that research has helped him to improve Nmap. I was lucky enough to attend, and even got to chat with him briefly and get a signed copy of his new book.
Anyway, after receiving numerous complaints over the years regarding performance, he did some colossal scans of the Internet in order to see how Nmap handled extremely large address ranges. What follows is a collection of the most interesting features he added, and information he learned, while doing his research.
First off, in case you want to test out some of these features as well, you’ll need to get the version of Nmap that he was using during this presentation. The current, stable branch does not have much of this functionality. You can get it via SVN like so:
svn co --username guest --password "" svn://svn.insecure.org/nmap-exp/bhdc08/
Then build it the standard way:
./configure
make
make install
One of Fyodor’s main focuses was improving Nmap’s speed through improved efficiency. One of the best ways to do this is to allow for scans of fewer ports, but this requires that you choose those ports carefully so as to miss as little as possible. So what he did, through trial and error and tons of scans, was figure out the most frequently open ports on the Internet.
Here they are for each protocol:
80
23
22
443
3389
445
139
21
135
25
137
161
1434
123
138
445
135
67
139
53
Ok, so now that we know what the top 10 ports are, wouldn’t it be cool to be able to scan based on them? And what if we wanted to scan the top 50? Or the top 100?
Fyodor has built this in with the --top-ports option. It’s wicked nice, and you invoke it like this:
nmap –top-ports 100 $target
And of course, 100 is just an arbitrary number, so you could just as easily do this:
nmap –top-ports 3000 $target
As you increase this number you obviously gain more and more accuracy, but because the ports are organized according to the most commonly found on the Internet, you can scan relatively few and still have good chances of finding everything open.
Stats from his presentation on TCP port efficiency using --top-ports:
–top-ports 10: 48%–top-ports 50: 65%–top-ports 100: 73%–top-ports 250: 83%–top-ports 500: 89%–top-ports 1000: 93%–top-ports 2000: 96%–top-ports 3764: 100%
This means for just curiosity scans I can go with --top-ports 1000 and get roughly 93% accuracy in a fraction of the time.
Do like.
Another feature that he’s been wanting to add for a while is rate limiting by packet count. He actually found a need for this when he was doing his research. He started some of his first scans and got a call from his ISP. They thought he’d been hacked.
He got it worked out, but he decided it was a good idea to be able to set a threshold for how hard you hit the network you’re scanning from. And here it is:
nmap –max-rate 1000 $targetnmap –min-rate 500 $target
This thing is awesome; when it shows you that a port was open or filtered or whatever—it shows you the reason it thought so.
Interesting ports on scanme.nmap.org (64.13.134.52): Not shown: 994 filtered ports Reason: 994 no-responses PORT STATE SERVICE REASON 22/tcp open ssh syn-ack 25/tcp closed smtp reset 53/tcp open domain syn-ack 70/tcp closed gopher reset 80/tcp open http syn-ack 113/tcp closed auth resetNmap done: 1 IP address (1 host up) scanned in 4.21 seconds
This will show you what the packets look like that you send and receive, with a handy little "sent" and "received" marker.
nmap –packet-trace -p80 danielmiessler.com
Get a weekly breakdown of what's happening in security and tech—and why it matters.
SENT (0.1160s) TCP 204.11.219.126:40117 > 204.11.219.126:80 S ttl=40
id=52313 iplen=44 seq=2829670227 win=1024
RCVD (0.1160s) TCP 204.11.219.126:40117 > 204.11.219.126:80 S ttl=40
id=52313 iplen=44 seq=2829670227 win=1024
RCVD (0.1160s) TCP 204.11.219.126:80 > 204.11.219.126:40117 SA ttl=64
id=0 iplen=44 seq=2909000595 win=32792 ack=2829670228
Interesting ports on danielmiessler.com (204.11.219.126):
PORT STATE SERVICE
80/tcp open http
Nmap done: 1 IP address (1 host up) scanned in 0.13 seconds
You can now add the -traceroute option to your scan and Nmap will pick a port and traceroute to the target host over that port.
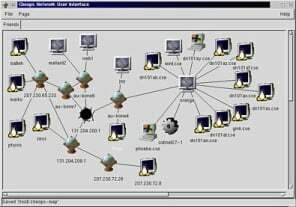
You heard me right. The latest version of Zenmap (bhdc08) now actually has a tab for creating maps like Cheops. The one above is an actual old Cheops screenshot because I don’t have X installed on the box running bhdc08, but you get the idea.
Ndiff is a sick little tool that compares Nmap XML files and produces XML or YAML formatted difference files. In other words, you can regularly scan your networks with Nmap and use Ndiff to not only tell you when new boxes pop up on (or drop off of) the network, but it’ll also tell you when new services are added or deleted to the boxes you already know about.
Brutally nice.
svn://svn.insecure.org/nmapexp/ndiff/ (same credentials as above)
An über version of Hobbit’s classic. Supports SSL, IPv6, connection brokering, proxies, shell execution, and tons of other stuff.
svn://svn.insecure.org/ncat (login: guest/guest)
If you’re not using this yet, you should probably get that way. Remember, it’s not just port scanning; you can actually check for vulnerabilities using this. Here’s one from his presentation that checks for DNS issues:
nmap -PN -v -sU -p53 -T4 –script=dns-test-open-recursion,dns-safe-recursion-port.nse,dns-safe-recursion-txid.nse dns-1.blackhat.com archimedes.shmoo.com
I’ll be adding these options, as well as a ton of additional new functionality, to my Nmap tutorial/primer located at https://danielmiessler.com/study/nmap/.
But no matter what you do, go get a copy of Fyodor’s new book. It’s a must.:
[ Nmap’s Home Page | insecure.org ][ Fyodor’s Blackhat Presentation | insecure.org ][ My Nmap Tutorial / Primer | danielmiessler.com ][ My Study Page | danielmiessler.com ]