PayPal and Two-Factor Authentication: A “Weakest Link” Case in Point
I am an enthusiastic > user > of the Verisign PIP > two-factor authentication service. It’s a system that allows you to add additional security to sites that support OpenID > by adding a one-time-password as a second factor of authentication.
So, even after you’ve authenticated to sites like e-Bay > and PayPal > (many big sites support it), you are prompted for a second value as seen below on PayPal:
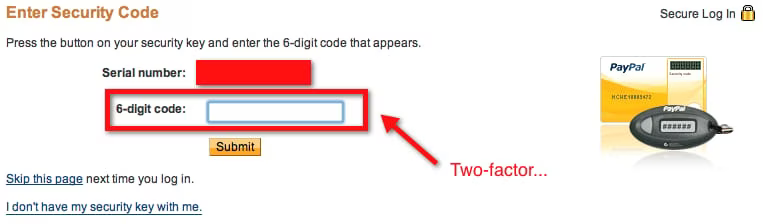
With only a quick look, this seems pretty cool. I’m being asked for a second factor of auth–even after I’ve logged in! But hold on a second. What’s this stuff at the bottom?
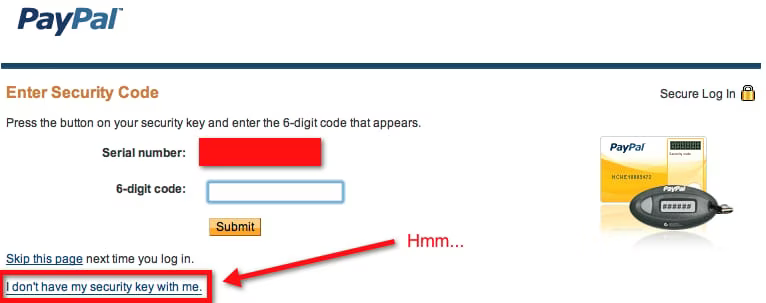
So let’s see what that leads to–probably some sort of high-speed out-of-band deal. Ouch. It gives you standard "forgot my password" options.
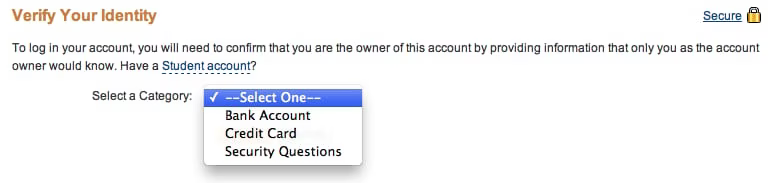
And if you pick the last one on the list, you get decade-old security, i.e. user-controlled secret questions.
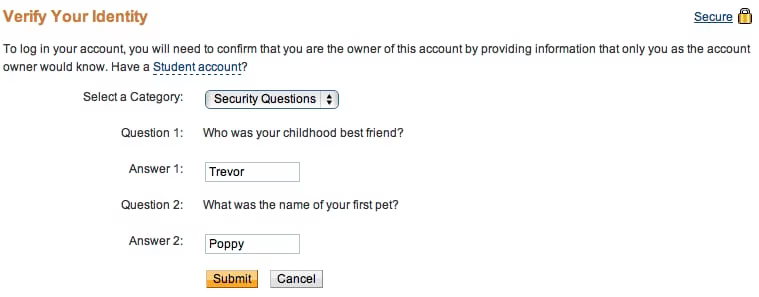
Great, my double-bolted titanium front door just got bypassed by having nothing but a screen door on the patio. All that coolness…all that security–gone. PayPal is giving the attacker an option: either bypass a two-factor authentication system, or, guess the name of my high school.
And yes, I realize that this all takes place after initially authenticating with a standard password. But if PayPal is going to make a big deal about partnering with Verisign to implement two-factor authentication, they shouldn’t implement it in a way that effectively makes it an illusion. Give people the option to disable simple questions and to require an out-of-band method for reset.
Something. Anything. Just not this. ::
[ A reader has correctly pointed out that the issue is with PayPal, not with Verisign, as PayPal is the one providing the bypass. I’ve updated the title and closing comments to make that more clear. ]