Innovative Security Products (2016 Edition)
One of the highest value events at RSA every year is the Innovation Sandbox, where companies are given just a few minutes to pitch their company’s product.
You might expect the companies to be saying the same things in different ways, but when you get to the Top 10 competitors the ideas are usually quite fresh.
Let me tell you about a few that I really like:
Illusive is a product that places thousands of false paths all over your production network that can only be seen by malicious actors, and when they are taken you get alerted | [ Video > ] I love the idea of malicious and benign actors seeing the world differently, and then alerting on the paths that the malicious ones take the moment they move. And that’s what is basically happening here. You have more ways to go down the wrong path if you’re malicious, and it’ll be noisy when you do make a move. Unfortunately, noisy doesn’t help most companies, since they’re not equipped to listen or respond.
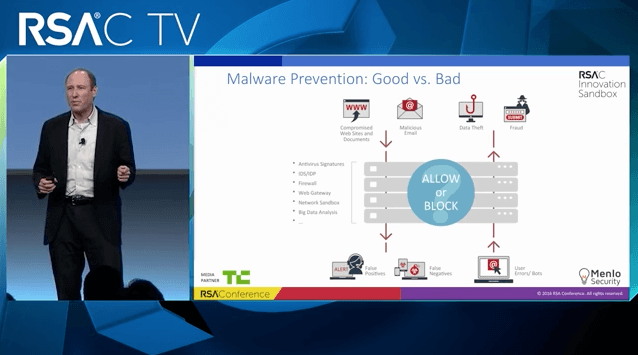
Menlo basically proxies and detonates every single aspect of a technology stack and only provides the real client with benign, sanitized output | [ Video > ] I love this approach because it goes back to the original concept of proxying. You assume the worst of every request, you drop it on the floor, and make your own that you know is legit. This does the same by providing only known-good content to the actual clients. I worry thought that this is likely to be quite slow in the beginning, and will likely only work for certain types of services.
Skyport is a virtualized security architecture that puts your app, with no changes, into an environment that secures the app from layer 2 to layer 7 | [ Video > ] I love this because you can just drop your app in and get the value of filtering at the various layers. There are likely to be some significant performance issues as well as concerns around privacy if you’re seeing every single thing going in and out of an app. And if you’re not, you’re not getting as much of a benefit.
SafeBreach performs constant real-world attacks on the network in order to validate your controls from an attacker perspective | [ Video > ]This is fascinating as a pitch. Truly. But I’d love to see more about how it works in the real world before I can get overly excited.
Phantom is the connective tissue that links all the various pieces of security functionality, from every product you have installed, into an automated workflow | [ Video > ]This is brilliant stuff, but I am worried that it requires a maturity and cooperation in the industry that isn’t quite there yet. Definitely what we should be thinking about though, to get the value from all those various products. Also love that the runreading are publicly hosted.
Prevoty does extremely high-speed application security filtering within the application’s runtime [ Video > ]Love the LANGSEC approach here, which offers tons of performance. Eager to see it expand to address more types of attacks.
Bastille is a hardware and software system that performs security filtering on IoT systems | [ Video > ]Unbelievably needed, but there are some significant limitations on what can be filtered based on what it can and cannot see, as well as on what types of events it should be alerting on or preventing.
—
Keep in mind I’m not endorsing these products. I’ve not used them or otherwise had their efficacy demonstrated to me.
But what I can say is that I’ve seen a million "me too" products, and these deserve some attention for their fresh approaches to solving infosec problems.
Notes
If you guys know of other products I should add, hit me up and I’ll add them. If you could include a summary like this, with a video link, that’ll make it even faster. Thanks!