A Guide to Information Security Certifications (2020 Update)
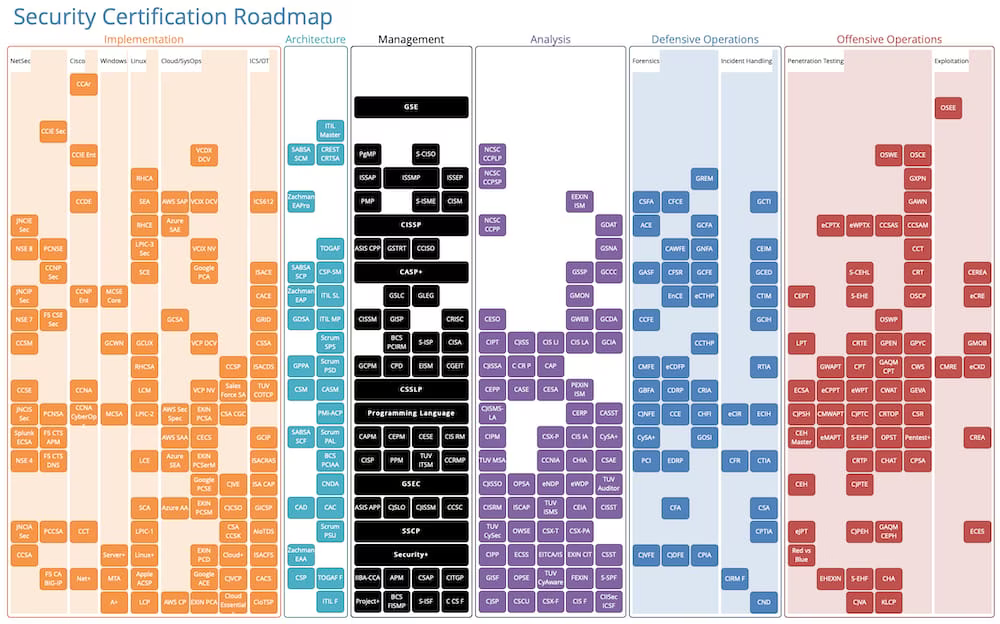
Many people are confused by the massive number of information security > certifications available today. Some people already have one or more and are looking to expand, while others are just getting started with certification and need a place to start. This guide aims to help with both scenarios.
I’m going to highlight a few of the certification options and offer a couple of recommended paths for professionals in various stages of their careers. I’ll be rating each credential based on the criteria below:
I have held only the CISSP, CISA, GCIA, GSEC, and Security+ credentials.
Who should be pursuing it
The company who runs the cert
The difficulty of the exam
Technical respect in the industry
HR respect in the industry
Requirements to get the cert
Cost of the cert
Additional comments I have on the credential
Numbers are on a scale from 1-10.
Security+
Who: People getting into the infosec field, regardless of future specialization. If you’re just starting out and looking for your first security cert, this is it.
Company: CompTIA
Difficulty: 4
Technical Respect: 4
HR Respect: 6
Requirements: None.
Cost: $339
Comments: I recommend this certification to a lot of people just because it’s such a good overview of the academic parts of security. It’s like a miniature CISSP. I also recommend it to people who are trying to figure out if security is something they might be interested in. If you look at a Security+ study guide and don’t find anything interesting, you might not find the field entertaining either.
SSCP
Who: People who already have the Security+ and who aren’t able/willing to take the CISSP yet for some reason
Company: ISC2
Difficulty: 6
Technical Respect: 4
HR Respect: 3
Requirements: One year in the security industry.
Cost: $250
Comments: I don’t think this is (in 2020) a great cert anymore. It used to be that this is what you should do before taking the CISSP, but now the Security+ is so good that you might as well just do that one and go right into the CISSP. You can take the CISSP and pass it even if you don’t have the time yet, and then get the cert once you get the required time in the industry. You can check this by doing a job board search for Security+, CCSP, and CISSP.
CISSP
Who: Anyone with 4-years plus of experience in the field who wants
Company: ISC2
Difficulty: 6
Technical Respect: 4
HR Respect: 10
Requirements: One year in the security industry.
Cost: $250
Comments: As bachelor’s degrees have become less important in the security industry, the CISSP has become more important. This is because there are so many people graduating college with no security knowledge whatsoever, and the CISSP at least makes you cram learn some basics. This cert has become the 4-year degree of infosec, especially in much of Europe. If you’re only going to get and maintain one general security certificate, it should be the CISSP.
Previous notes on the CISSP (from 2014)
Pros: The CISSP is the undisputed king of infosec certifications. It’s the first infosec cert to receive ISO recognition — a great achievement not only for the certification itself, but also for the field as a whole. It commands a great deal of respect in many IT circles (and HR circles), and this can be clearly seen via job search results. It can help your chances greatly of getting high-paying jobs, and is an excellent addition to any resume. If you are only going to get one infosec certification, it should be the CISSP.
Cons: While the CISSP is the king of information security certifications, it suffers from being thought of as something it isn’t. Many still mistakingly view it as proof that someone is an expert in the field, and that couldn’t be farther from the truth. ISC2 has explicitly stated in the past that the test is designed to test a broad base of general knowledge, not to certify someone as a master of their field. Also, despite the rumors of impossibility, the exam also supports over a 70% first-time pass rate.
Comments: The CISSP is a great exam because it is not easy to take (experience in the field is required ), and once you are able to take it, it’s administered in a professional, controlled environment. What people fail to realize is that it’s geared for high-level security professionals such as managers. Obviously, anyone can go for it, but it’s not designed to test technical skills or the ability to actually perform in the trenches of an infosec environment. It’s a test designed to ensure that you are familiar with some basic concepts; it’s when people lose sight of this that the confusion starts.
As for the difficulty factor, I started studying for mine on a Monday (a "bootcamp") and passed the exam on that Saturday — and that’s with zero previous exposure to the CISSP study material. A buddy of mine just got his as well, and his study consisted of around 2 weeks of passively glancing at the material while leveling his WoW character. Again, that’s not to say it’s not an excellent certification to have, it’s just that the difficulty (or value) should not be overestimated.
CISA
Who: Anyone going into an auditor-type role, or who wants to round out their certifications with an auditor skillset
Company: ISACA
Difficulty: 5
Technical Respect: 2
HR Respect: 6
Requirements: None.
Cost: ~$600
Comments: The CISA credential is ideal for anyone already doing, or looking at getting into information security auditing. If you’re not familiar with auditing, think of accounting. It’s basically ensuring that proper processes are in place and that people (and technologies) are doing what they’re supposed to be doing. Information security auditing, as a field, is becoming more and more needed. Due to the continued release of new legislation, along with the requirement to enforce what already exists, this will do nothing but accelerate. Adding a CISA to your resume is definitely a good move, and should probably be your second or third certification, right after your CISSP (unless you go for your GIAC first).
CISM
Who: Anyone going into an auditor-type role, or who wants to round out their certifications with an auditor skillset
Company: ISACA
Difficulty: 5
Technical Respect: 2
HR Respect: 6
Requirements: 3 Years of Security Management Experience.
Cost: ~$600
Comments: The CISM credential is for information security managers. It’s for those who wish to show that they can manage an enterprise information security program.Pros: The credential comes from ISACA, which is a respected organization, and the position of information security manager is so important to companies that any credentials that speak to one’s competence will be helpful. Anyone wanting to get into an ISM position needs to be looking at this credential, but it doesn’t have the power of CISSP in my view. I think that out of the two big ISACA certs, the CISA offers more of a punch, albeit not necessarily for managers.
GIAC Certs (GSEC, GCIA, GCIH, etc.)
Who: Anyone looking to study and certify in some technical areas of security, or to round out there certifications with some technical options.
Company: GIAC
Difficulty: 6-9 (The GSEC is a 6, the GSE is a 9)
Technical Respect: 7
HR Respect: 7
Requirements: Most have no requirements, but the GSE requires that you have many other GIAC certs, and some at the Gold level.
Cost: ~2,000 for most tests
Comments: GIAC tests are the default now for technical certificates. They’re the most known and the most respected by the most people. Offerings like the Offensive Security tests are more elite, but lesser-known. The pure advantage of the GIAC certs is their notoriety and their breadth. You can basically get a GIAC cert in anything from web security to forensics to packet analysis, which is not something you can do with any other organization. Basically, if you’re the type who likes to collect certs, you should have at least one of these, starting with the GSEC. The other, non-GSEC certifications represent the "hardcore" SANS offerings. They are more in-depth and difficult than the GSEC, and they focus on one area specifically. GCFW is for firewalls and VPNs, GCIA is for IDS/IPS, GCUX is for Unix security, GCFA is for forensics, and GCIH is for incident handling. These are just a few of those that are offered, and these are geared towards veteran infosec professionals who have already specialized in an area. If this sounds like you, these certs are the way to go.
OSCP
Who: People looking to do penetration testing > as a job.
Company: Offensive Security
Difficulty: 9
Technical Respect: 10
HR Respect: 9
Requirements: You must have paid for the Pentesting with Kali course.
Cost: ~$800 dollars for the Kali course.
Comments: OSCP is among the most respected security certifications in the world, with an extreme technical focus. The first thing that distinguishes it is that it’s hands-on, meaning you must actually do some hacking to pass. It’s not multiple choice. It involves navigating through a lab and capturing flags that take you through to the end. There are many at the highest level of pentesting who think the test is easy, or a sham, or whatever, but that’s the case for many canonical exams once you’ve been in the industry for long enough. If you’re looking to land a pentesting role without having that much experience, this is one of the best certs you can get.
CRT
Who: People looking to do penetration testing > as a job, especially outside of the United States.
Company: CREST
Difficulty: 10
Technical Respect: 10
HR Respect: 9
Requirements: You must have paid for the Pentesting with Kali course.
Cost: ~$600
Comments: The CRT certificate from CREST is like the European OSCP, and the two organizations now have a relationship that allows you to get the CRT if you have already passed the OSCP and another smaller exam. The CRT by itself also requires a practical exam, and it’s considered to be harder than the OSCP’s, with less time to do it. Bottom line: if you want to be papered up in pentesting, you’ll want the OSCP and the CRT by CREST.
Recommended certifications for different career paths and levels

Ok, so now let’s get to the recommendations. Here’s what I’d recommend for some different combinations of focus and experience.
Just Starting Out, Not Sure What to Do: Security+
Just Starting Out, You Want to Be a Manager: Security+, CISA, then CISSP after 4 years.
Just Starting Out, You Want to Be a Pentester: Security+, GSEC, GPEN, and get involved in the Bounty Community. Then OSCP and/or CRT if you want more paper after you have experience.
After a Few Years in Security, Looking for Promotion/Pay: CISSP, CISM, some GIAC certs to get more technical exposure, and get involved in the Bounty Community. The biggest thing for promotion, when it comes to certs anyway, is probably CISSP.
The Basic All-arounder Cert Set: CISSP, CISM, GSEC. This gives you the 4-year degree of certs, the auditor cert, and the basic technical cert. Salt as desired afterward.
Comments on certification vs. experience
This guide is about certifications, but I want to be clear that experience has—in my opinion and many others I know in the industry—now overtaken both certifications and education as the most desired trait.
If you have hardcore experience, and the portfolio and artifacts to highlight it, you’re not going to really need certifications. There are exceptions, like government or stodgy jobs that are kind of stuck in time. But in general, experience is now king.
Hiring managers have been burnt too many times by people who have every degree, or ever certification, that exists, and who simply cannot do the job.
Remember, certifications and degrees are proxies. They’re stand-ins. They are artifacts designed to signify knowledge. But nothing does that better than being able to show you’ve successfully done that exact job in the past.
Summary and recommendations
So now here are my overall career recommendations.
First, read my guide to building a successful career in information security >.
Remember that degrees and certifications are what you need when you have nothing else. That’s all the hiring manager and HR can go on if you have no portfolio or history.
That being said, work on your experience and portfolio as quickly as possible so that certificates become sprinkles on your ice cream instead of the ice cream itself.
Welcome to the field. And good luck to you.