AI's Morose Mania
The more excited we are as developers, the more we have to worry about knowledge workers

I saw a tweet recently by Robert M. Lee—a highly respected ICS Security professional in the industry.
When folks put "ICS" in the category of "IOT" it conflates the systems, purpose, value, and risks of separate communities. There’s important differences between a robot arm in a car manufacturing plant and your internet connected doll even if both have default passwords.
I am a mid-tier ICS Security person, by the way. I’m experienced with it, and an expert compared to most security people, but I’m a non-expert compared to the people fully focused on it like Robert.
I see his point, and I think it’s valid, but I worry that some people who are not experts in IoT or ICS security might not get the nuance. The part I want to quibble with is this bit:
When folks put "ICS" in the category of "IOT" it conflates the systems, purpose, value, and risks of separate communities.
Robert M. Lee
Robert M. LeeI almost completely agree with this statement—but with a caveat.
Basically, I do believe that ICS is a category of IoT—if you define IoT a certain way. As usual, so many of these discussions come down to definitions. And this isn’t going to be a rant about how my extremely detailed and specific definition is the most accurate, and how Robert’s or anyone else’s is specifically and technically incorrect.
I think we actually need to head the opposite direction when it comes to these definitions and discussions. I think the definition we should be using for IoT, when we’re talking with non-experts and the public at large is something like, "The process of connecting everyday objects and systems to networks in order to make them globally available and interactive."
For most people, IoT can best be thought of as the process of connecting everyday objects and systems to networks in order to make them globally available and interactive.
I believe this definition does a lot of work for us.
Most importantly, it unifies the risks around everyday IoT, ICS, and IIoT. It makes it clear that the primary source of risk for all IoT is the fact that there are many sensitive things that happen in this world, and that it’s inherently a really big deal to start connecting those functions to networks.
Get a weekly breakdown of what's happening in security and tech—and why it matters.
Even the Internet of Shit can be dangerous if it’s insecure and grants access to something or allows an attacker to steal resources, e.g., the fish plaque connected to the cloud that grants access to your network.
This is true of car robot arms, baby monitors, thermostats, and almost every type of IoT we one can imagine. That is the unifying component—going from analog to digial, from isolated to connected, and from static to interactive.
Now, that being said, I absolutely agree that this unification has limits, and that—like Robert said—it’s simultaneously critical to make distinctions between the various types of IoT. But once we accept what’s similar, I think it’s easier to make those lines clearer for people.

I think it comes down to magnitude of impact assuming something were to go wrong. If your fish plague gets compromised, an attacker might use your bandwidth to create fake ad clicks, or they might try to pivot and install ransomware on your systems at home.
But if a major dam’s SCADA system is compromised, well, millions of dollars of property could be lost, people can be hurt and killed, and it can have a major effect on livelihoods and economies. That’s a major difference worth calling out.
So I guess what I’m saying is that perhaps we should use a broader, more approachable definition of IoT that unifies underneath the basic concept of old=disconnected=lower risk, and new=connected=higher risk. And then from there we can make the separations within IoT of the types according to impact. Perhaps something like the following:
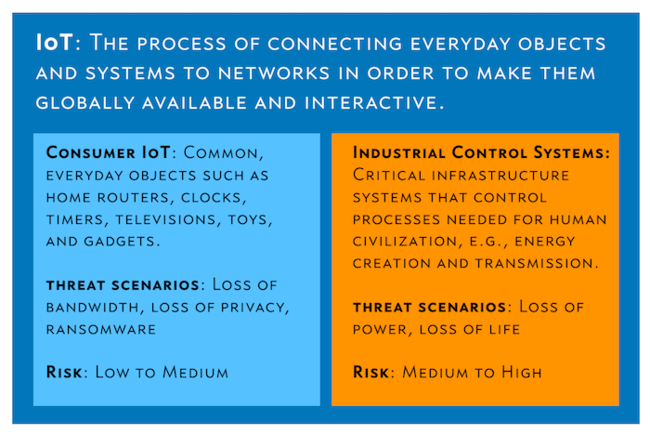
A conceptual differntiation between IoT, Consumer IoT, and Industrial Control Systems
Eager to hear any feedback.
I think the distinction is minor, but important.