The Difference Between Decompilers, Disassemblers, Debuggers, and Hex Editors
For people looking to get into reverse engineering, the barrier to entry can be fairly steep—starting with the terminology. Here are the differences between a few key tools you will encounter on the path.
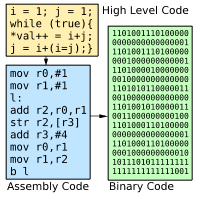
Decompilers reverse binaries into higher-level languages, like C++.
Disassemblers reverse binaries into assembler language.
Debuggers allow you to view and change the state of a running program.
Hex Editors allow you to view and edit the contents of a binary.
Another set of things to know is the different kinds of programming languages. Here they are—from low to high levels of abstraction from the CPU.
Modern languages like Python and Ruby are considered high-level languages, but are functionally a level above.
Machine Code is the 1’s and 0’s executed by a CPU.
Assembler is the next level up, and is the first human-readable level, but just barely.
High-level—also called Compiled—languages include C and C++, and they’re the first level of functionally readable code.
Interpreted Languages are languages like Perl, PHP, Python, and Ruby, which require an environment to run them, trade readability for speed.
Bytecode Languages are languages like Java and .NET, which are cross-platform like Interpreted languages, but with similar readability and speed to compiled languages.
Summary
To go from binary to assembler, use a disassembler.
To go from binary to higher lanugage, use a decompiler.
To edit a particular part of a binary’s contents, use a hex editor.
To interact with an application as it’s running, use a debugger.