Purple Team Pentests Mean You’re Failing at Red and Blue
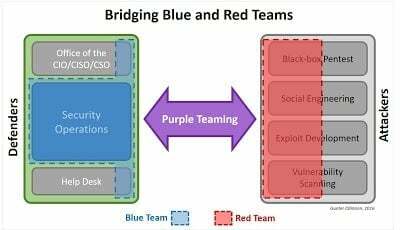
A Purple Team Pentest should be thought of as a dynamic amalgamation of Red Team and Blue Team members with the purpose of overcoming communication hurdles, facilitating knowledge transfer, and generally arming the Blue Team with newly practiced skills against a more sophisticated attacker or series of attack scenarios.
http://technicalinfodotnet.blogspot.com/2016/11/the-purple-team-pentest.html
http://technicalinfodotnet.blogspot.com/2016/11/the-purple-team-pentest.htmlThis article claims that Purple Teams should make it so that Red Teams share their knowledge with the Blue Team. So basically a "Purple Team Pentest" would be one in which that sharing occurs.
Ok. That’s one way of looking at it. Let me give you another.
If you have a Red Team that doesn’t share information with the Blue Team, you don’t have a Red Team. What you have is a band of marauders who think they’re better than everyone else and don’t understand their actual purpose.
The term "Red Team" came from the military, and its best definition is:
An independent group that challenges an organization to improve its effectiveness.
https://en.wikipedia.org/wiki/Red_team
https://en.wikipedia.org/wiki/Red_teamSo if the purpose of a Red Team is to improve the effectiveness of something, what do we think that something is?
It’s the company they’re testing, a.k.a., the Blue Team.
These terms are getting hijacked and mangled by sales and marketing teams, and it’s far past time to push back.
Good Red Teams share data with their Blue Teams—that’s what they’re there for. Purple Teams, if they exist, should be temporary while this is being fixed from a previous, broken implementation where no sharing was taking place.
For a breakdown of different types of information security assessments, I humbly suggest my own resource on it. I’ve put a lot of thought into these definitions over the years, and I have yet to find better ones.
Link: Information Security Assessment Types
If you do have better definitions for these, please let me know. And if not, let’s use the ones we have instead of letting sales types make up new ones that confuse the customer and everyone else.