Not All MFA is Equal, and the Differences Matter a Lot
People are starting to get the message > that text/SMS is a weak form of multi-factor authentication (MFA). Fewer people know that there’s a big gap between the post-SMS MFA options as well.
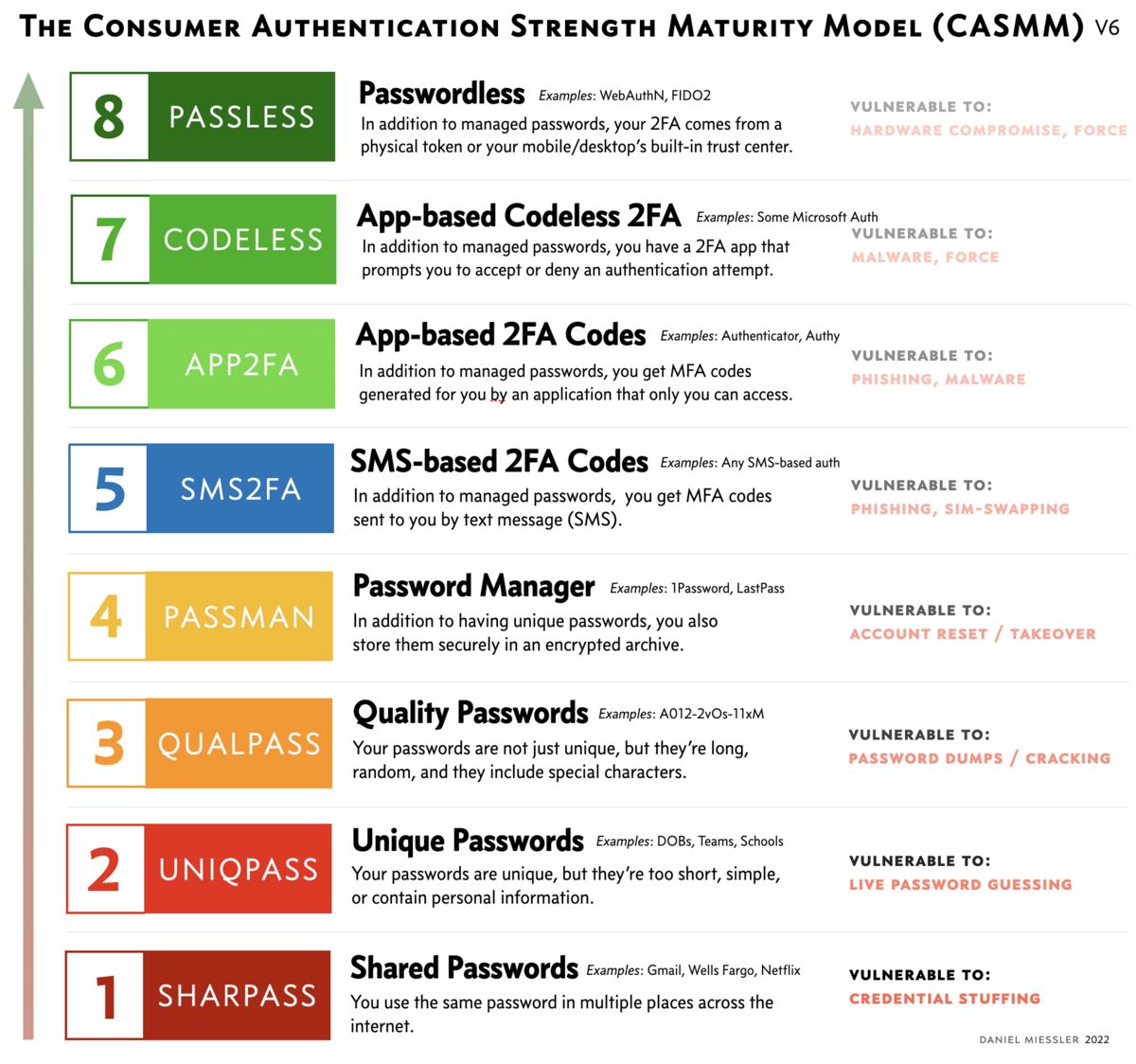
As I talked about in the original CASSM post >, there are levels to this game. In that post we talked about 8 levels of password security, starting from using shared and weak passwords and going all the way up to passwordless.
This post will explain the main difference in the higher levels—specifically, what makes Level 8 so much better than 7 and below?
The answer is simple, actually—phishing.
A growing percentage of malware packages now include prompts for not only a username and password, but also an MFA code. This means traditional MFA is becoming increasingly useless against phishing in the real world.
The problem isn’t how you got an MFA code—the problem is giving you an MFA code in the first place.
And it doesn’t really matter how you got that MFA code. It might have been a text, or it could have been something "strong", like a mobile authenticator app like Google Authenticator or Authy. However you got it, you now have it, which means you can now type it into a text field owned by a bad guy.
So that raises the question: is there a type of authentication that protects against this? In other words, is there a type of MFA that’s resistant to phishing? The answer is yes.
FIDO stands for Fast Identity Online, and it uses the Universal Authentication Framework (UAF) and Universal Second Factor (U2F) protocols. The systems use public-key cryptography and a physical access token. The private key is stored on the token and kept with you, and the public key is stored with the services you want to authenticate to.
You can’t phish an MFA code that doesn’t exist.
When you authenticate, you prove to the client/token that you are you (fingerprint, PIN, voice, etc.), and the client creates a signed request that’s sent to the service. That request is decrypted and authenticated using the public key, which proves the request was made using the private key, and you are then authenticated.
FIDO2 / WebAuthn is the passwordless version of FIDO, and the passwordless part is critical here. It completely changes how authentication is done.
Instead of you being presented with a website—which could be malicious—that you then enter credentials into, you instead navigate to the legitimate website like usual, and you get prompted to authenticate.
You then authenticate using your physical token, which you keep with you, by touching it for example. Or using your face or whatever. And when that happens (this is the brilliant bit), your local token creates a request and signs it with your token’s private key…
…and then sends that specifically to the exact, legitimate URL associated with the token!
That’s the magic. When you enrolled the token with, say, Gmail, the token collected the official URL for Gmail, so it can only send authentication requests to that URL!
The best part of this entire flow is that there’s nothing to type. All you did was touch something or look at your device. Everything else happened in the backend automatically.
And since there’s nothing to type there’s also nothing to phish!
This is why passwordless is the highest level of the CASMM Authentication Maturity Model >. It disrupts the standard phishing workflow by completely removing the step of manually creating and entering MFA codes.
Summary
TL;DR: The feature that improves MFA the most is the avoidance of manual MFA codes that must be input somewhere by users, because that is the step that is exploited during phishing attacks.
Not all multi-factor authentication is the same in terms of providing protection to consumers.
The primary interactive threat to consumers is phishing, and malware is now gaining the ability to phish for SMS and App-based MFA codes.
The way to address this is to move to the top level of the CASMM Authentication Security Model >, which allows you to authenticate without having to deal with MFA codes, which is the step that phishing attacks are based on.
FIDO2 and WebAuthn are implementations of this "passwordless" authentication model that uses PKI in the background to automatically send secure requests to—and only to—a pre-arranged and authorized URL in the background.
Because this happens securely in the background, this system completely removes the step of MFA codes given to you by text or authenticator apps, which can then be entered into a malicious website or given over the phone.
And since you don’t have MFA codes anymore, those MFA codes cannot be fished anymore.
Consider switching to FIDO2 / WebAuthn based security tokens for your most critical accounts such as your email account, banking, taxes, etc.
Get started with FIDO2/WebAuthn >> >
Notes
Please remember, and share with your friends and family, that any 2FA is still significantly more secure than password alone. So while you should be moving beyond SMS and legacy MFA codes, if you have the choice of doing nothing and doing SMS-based MFA, you should still do it.
There are other app-based MFA methods that also work transparently in the background to authenticate the user, and those are also at Level 8 because they avoid giving the user a code and are therefore "passwordless".
There are attacks against this stronger auth, but they’re easier to avoid and harder to pull off, e.g., 1) getting you to enroll your token to a fraudulent site, or 2) breaking PKI in some way that makes it look like the auth request is being sent to the legitimate URL when it’s actually going to an attacker.